By adopting these safety measures, users can better protect themselves while exploring the 0day onion network, ensuring their experience remains secure and private. For the biggest bulbs, plant short-day onions in the fall—overwintering these varieties will allow the plants plenty of time for vegetative growth before transitioning to bulb development. Accessing and navigating the 0day onion network requires careful attention to safety and security measures. Understanding the world of cyber security and digital anonymity requires familiarity with various concepts, among which 0day onion plays a significant role.
Ultimately, fostering a deeper understanding of the 0day onion landscape empowers individuals to better prepare for and respond to cybersecurity challenges. In conclusion, the exploration of 0day onion highlights the critical intersection of cybersecurity and the deep web. A 0-day vulnerability refers to a security flaw that is exploited by attackers before the software developers are aware of its existence, meaning there is no time to develop a patch. One major risk tied to 0day onion vulnerabilities is the potential for data breaches. 0day vulnerabilities, commonly referred to as “0day exploits,” represent unpatched security flaws that hover at the intersection of potential threat and opportunity in the cybersecurity landscape. In essence, it refers to a zero-day exploit that is shared anonymously via the Tor network, allowing users to access vulnerabilities before they are discovered and patched by developers.
- With more than 45,000 exploits1, EDB exceeds 0day.today’s offering of just under 38,0002.
- Get strategic cybersecurity insights in your inbox
- One major risk tied to 0day onion vulnerabilities is the potential for data breaches.
- Security professionals monitor the 0day onion space to stay informed about potential data breaches and protect systems against emerging threats.
- People join the 0day onion community for a variety of reasons, from learning the art of hacking to trading information about the latest exploits that can be leveraged for illegal gains in the black market.
Monitor competitor funding, hiring signals, product launches, and market movements across the whole industry. Tokyo Long White Bunching Onion Seeds – Heirloom, Non-GMO, Green Onion Variety Discover the exceptional Tokyo Long White Bunching Onion seeds, also known as green onion seeds, perfect for adding fresh flavor to your garden and kitchen. Onion plants are categorized into two groups based on the hours of daylight they need to grow properly.

In the ever-evolving landscape of cybersecurity, the term 0day onion has emerged as a significant concept among those familiar with underground hacking communities. This term refers to a unique blend of vulnerabilities and hidden information that can be exploited for malicious purposes. The "0day" aspect signifies vulnerabilities that are unknown to the software vendor or security community, while "onion" refers to the layered anonymity provided by the Tor network, commonly associated with clandestine activities. Understanding the dynamics of 0day onion can shed light on the complexities and dangers posed by contemporary cyber threats.
Understanding 0day Vulnerabilities

A 0day vulnerability is a security flaw that is exploited before the vendor has an opportunity to release a patch. This means that users are left vulnerable until a protective measure is established. Cybercriminals often seek these vulnerabilities to take control of systems, steal information, or launch attacks, making 0day onion a term closely related to these threats. The meticulous nature of finding such vulnerabilities requires immense skill and knowledge of various programming languages and security protocols.
The Role of Anonymity with Onion Routing
The term "onion" in 0day onion originates from onion routing, a method used to anonymize internet traffic. By encapsulating data in layers, similar to peeling an onion, users can navigate the web without revealing their identity. This feature is particularly valuable for cybercriminals who utilize the Tor network to share 0day exploits and vulnerabilities while evading law enforcement. The intersection of 0day onion highlights the dangers posed by individuals who exploit these vulnerabilities under the cover of anonymity.
Market Dynamics of 0day Exploits
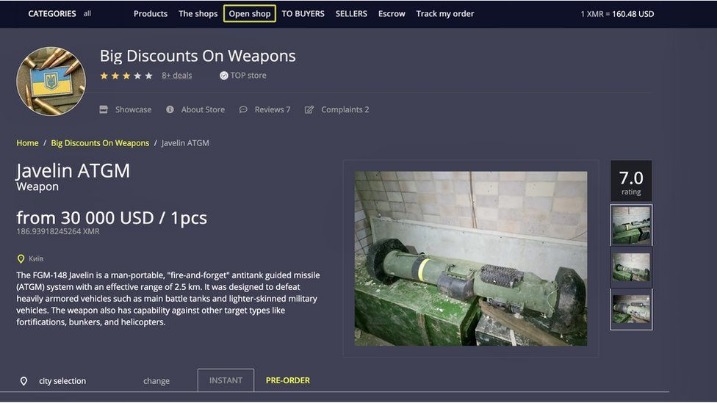
The market for 0day onion exploits is lucrative, with strong demand from various entities, including state-sponsored hackers, organized cybercriminal groups, and even legitimate cybersecurity firms looking to bolster their defenses. These exploits are often traded on dark web forums for substantial sums, creating a thriving ecosystem around 0day onion knowledge and tools. As companies scramble to patch these vulnerabilities once they become known, the race between attackers and defenders intensifies.
- The presence of 0day onion scenarios makes it imperative for cybersecurity professionals to stay updated on emerging threats and to implement robust security measures.
- The discovery and exploitation of software vulnerabilities within the Tor network, specifically targeting hidden services or “onions,” represents a high-stakes domain of cybersecurity.
- One of the primary future challenges involves the continuous arms race between security measures and malicious actors.
- All communications should be end-to-end encrypted, and metadata, often more revealing than the content itself, must be minimized through the use of anonymous networks and secure protocols.
- Get a live demo of our security operations platform, GreyMatter, and learn how you can improve visibility, reduce complexity, and manage risk in your organization.
- As soon as the day length is over hours, and your onions are planted in a good sunny spot, your onions will begin forming bulbs underground.
Consequences of Ignoring 0day Threats
Failure to address the risks posed by 0day onion vulnerabilities can result in severe consequences for individuals and organizations alike. Breaches associated with such vulnerabilities can lead to stolen data, financial losses, and significant reputational damage. Moreover, as we increasingly rely on interconnected systems, the potential impact of a single 0day exploit can reverberate across multiple sectors, emphasizing the need for robust cybersecurity measures against 0day onion threats.
Conclusion
In summary, the concept of 0day onion encapsulates the dangerous interplay between undiscovered vulnerabilities and the anonymity provided by the dark web. As cyber threats continue to evolve, understanding this intricate relationship can better equip individuals and organizations to anticipate and mitigate risks. Staying informed and proactive in the face of 0day onion vulnerabilities is crucial in today's digital landscape.